Penetration Testing: Why You Need It and What to Expect

Your organization has implemented specific cybersecurity measures to protect against breaches. You’ve put processes in place to thwart and detect malicious activity in your IT environment. But can you really be sure you’re doing enough to safeguard your company’s assets?
Without a clear understanding of your company’s response to a breach, it can be difficult to know if you’re taking all the necessary steps. It’s one thing to aim for security; it’s another to prove that your measures are effective when it counts.
Don’t wait for a hacker to test your systems’ security. Like a drill, penetration testing allows your organization to practice responding to real cyberthreats—without the financial and data risks.
What is Penetration Testing?
Penetration testing, also known as “pen” testing, is a proactive cybersecurity measure that entails launching a simulated cyberattack against your IT systems to identify vulnerabilities. The result of a penetration test is a report of findings that:
- Gives you assurance that you are secure
- Showcases items that need to be strengthened
What’s the difference between a penetration test and a vulnerability assessment?
Penetration testing and vulnerability assessments both identify weak points within your IT systems, but they have very different approaches.
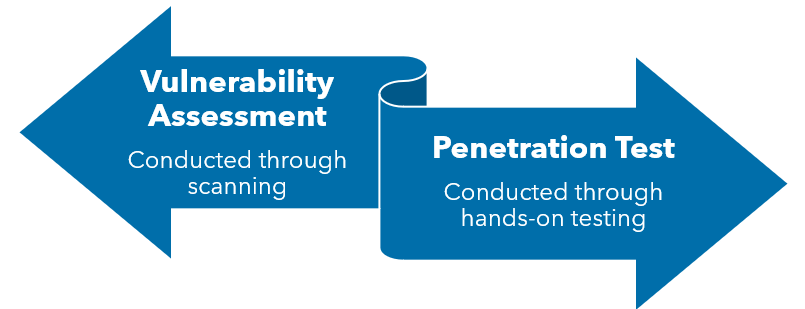
In a vulnerability assessment, potential threats are identified through software scanning. In a penetration test, a certified ethical hacker uses various applications and conducts hands-on testing by actually attempting to access your systems and data, which demonstrates the possible impact of a real breach.
What is an ethical hacker?
Ethical hackers are trusted cybersecurity professionals with expertise in a wide range of hacking methods used by cybercriminals. These experts are certified and trained to conduct testing on companies to demonstrate the potential impact of a real cyberthreat.
While some providers may claim to offer penetration testing services, many either outsource the testing to another vendor, have the testing performed by someone who isn’t certified, or state they are performing a penetration test by just using a tool. It is important to thoroughly vet your provider to know what type of penetration testing you are getting. Having an experienced certified ethical hacker conduct penetration testing services is particularly important because it ensures that the testing is done accurately and thoroughly.
How Does Penetration Testing Work?
While there are multiple penetration testing methodologies, you can generally expect any penetration testing process to include the following steps:
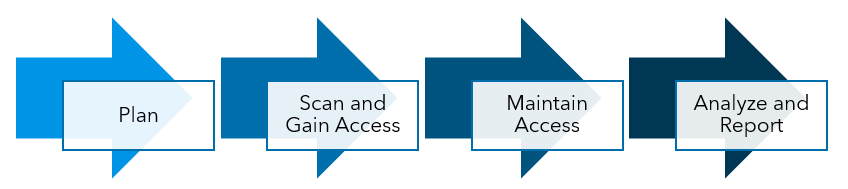
1. Plan
Before starting a penetration test, your ethical hacker will work with you to define the scope, limitations and specific goals of the testing. Your penetration testing services provider will also gather information about your company’s network and operations. They may also obtain data that is publicly available, such as news articles or employees’ social media accounts, to find usable targets.
2. Scan and Gain Access
In order to fully understand how the target application will respond to intrusion attempts, the ethical hacker may use both automated and manual processes to identify vulnerabilities that could allow them to gain access to your systems.
3. Maintain Access
When they have solidified their means of access, the ethical hacker will begin mimicking advanced persistent threats and exploiting the vulnerabilities identified. Just as with a malicious attack, the ethical hacker will move from vulnerability to vulnerability, gaining higher privileges to navigate even deeper into your systems to attempt to access sensitive assets.
4. Analyze and Report
When the testing is complete, the penetration tester will compile the results into a detailed report. All of the information in the report should be used to inform your decisions for improving and remediating your organization’s defenses against real-world attacks.
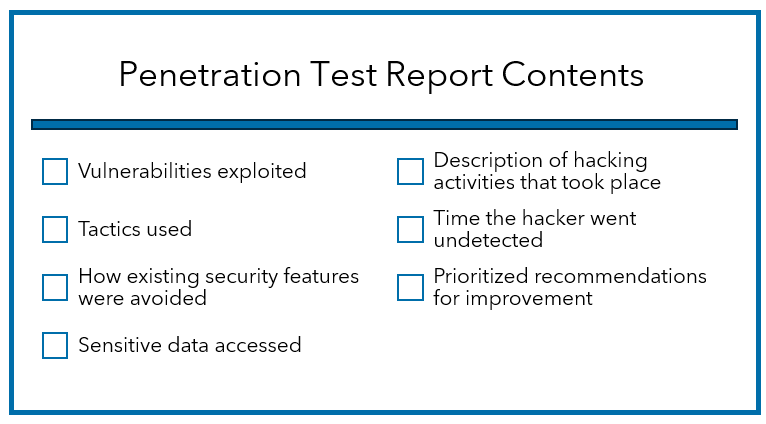
What Does a Final Report from Penetration Testing Services Include?
The final report provided after your penetration test should clearly detail the specific vulnerabilities your ethical hacker exploited, the tactics used and exactly how existing security features were avoided.
It should also document the ethical hacker’s report of the sensitive data accessed, descriptions of what was done while they were in the system and the amount of time the ethical hacker was able to remain in the system undetected. Finally, your report will provide prioritized recommendations for improving your organization’s security posture based on the testing experience.
Based on these findings, your penetration testing services provider can explain the overall status of your IT security and help you develop and implement a corrective action plan to address vulnerabilities.
How do I know if My Company Really Needs Penetration Testing Services?
Any company looking to improve its security posture and protect its assets can benefit from having a penetration test conducted.
A penetration test should be a top priority for your business. Especially if:
- you are experiencing increased cyberthreats
- you have experienced recent organizational changes
- your IT infrastructure is inherently more complex
or you just want peace of mind that you are taking the right security measures to protect your organization.
Penetration testing may also be advised depending on your organization’s regulatory requirements. It’s one of the cybersecurity measures strongly advised by GPDR and HIPAA, and it’s specifically mandated by PCI-DSS.
Improve Your Security Posture with Penetration Testing Services
When penetration tests are administered regularly and correctly, they can help you minimize security weaknesses, identify areas for improvement, promote regulatory compliance, and provide you with an opportunity to protect your organization’s reputation and prevent destructive breaches.
Penetration testing services conducted by third-party certified ethical hackers can uncover vulnerabilities that your in-house security team may unknowingly overlook. Start with choosing a reputable penetration testing provider that provides certified personnel to perform the test.
To learn more about penetration testing services and exactly how your company can benefit from them, connect with Warren Averett Technology Group.

