Ransomware and Municipal Governments: Risks, Impacts and Practical Responses

Ransomware is not a new problem for municipal governments. Cities like Atlanta, Baltimore and Riviera Beach made national news after getting locked out of their own systems, and the threat has only grown since then.
In July 2025, the city of St. Paul, Minnesota, declared a state of emergency after a ransomware attack shut down billing, emergency coordination and citizen services for more than two weeks.
The headlines come and go, but the threat has not slowed down. Ransomware groups are more organized, their tactics are more advanced and the consequences of a successful attack are worse than they used to be.
The first half of 2025 alone saw a 65% increase in ransomware incidents affecting government bodies compared to the same period a year earlier. Municipalities remain one of the most targeted segments of the public sector.
Understanding how ransomware works, why municipalities are particularly vulnerable and what practical steps can reduce risk is critical for any city or county leader responsible for protecting public systems and citizen data.
What Is Ransomware?
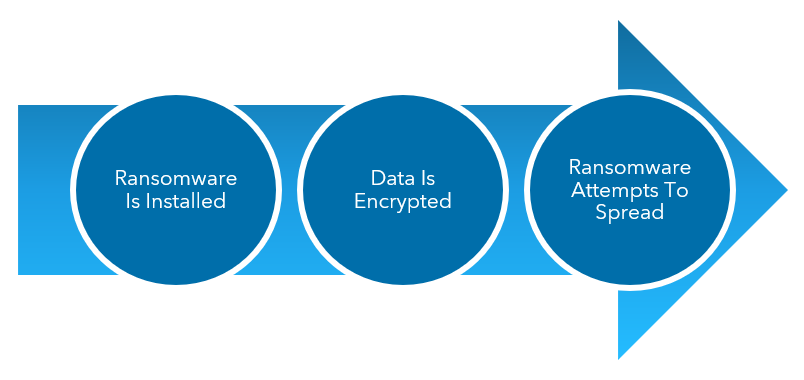
Ransomware is a type of malware. Once installed on a machine, it first encrypts (or locks) all of your data and then attempts to spread quickly to other machines on the network. Attackers demand to be paid a ransom in exchange for unlocking the data.
But the threat goes beyond the malware itself. Ransomware today is run like a franchise operation. Groups like Qilin, RansomHub and DragonForce operate Ransomware as a Service platforms where affiliates can launch attacks under a shared brand with shared tooling. That means more attackers have access to more sophisticated tools than ever before.
Why Municipalities Are Still at Risk
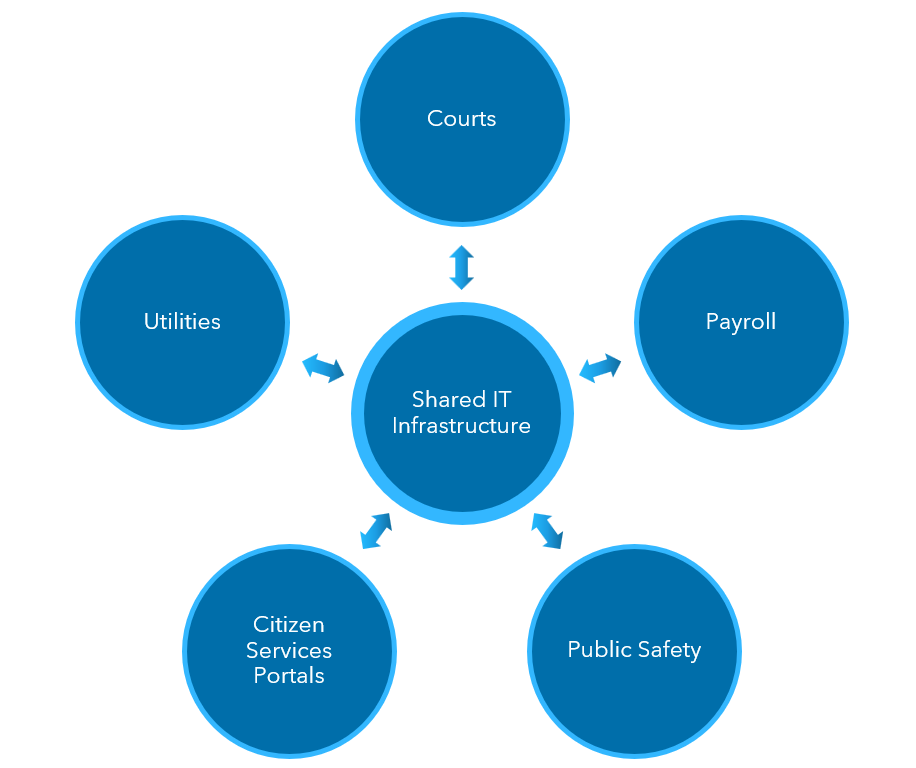
Municipal governments face a distinct ransomware risk because they provide essential services, operate with high public visibility and manage data that can’t be recreated or easily restored.
Data like court records, payroll and vital records are foundational to daily operations and legal obligations. So, when a municipality’s systems are disrupted, impacts show up almost immediately, and there is intense public pressure to get systems back online fast, even when ransoms are not paid.
The structure of the typical municipal IT function adds to the complexity. Systems are spread across departments, tied to vendors and state platforms, and constrained by staffing, budget and procurement realities that make upgrades slower and more complicated.
When an incident occurs, the fallout can trigger legal exposure, public scrutiny and long‑term trust issues, with ripple effects for schools, hospitals, housing authorities and local businesses. That combination of visible impact, limited flexibility and broad consequences makes ransomware a persistent and serious issue for cities and counties.
Between 2018 and 2024, 525 ransomware campaigns targeted U.S. government bodies resulting in more than a billion dollars in downtime costs alone.
How Should Organizations Respond if a Ransomware Attack Occurs?
In ransomware attacks, many victims assume that the most logical response would be to pay the ransom; a $300,000 ransom may appear to be a better option than a reputational hit and millions of dollars in recoverability expenses.
But even if you pay the ransom, there’s no guarantee that the data will be unlocked. In some ransomware attacks, the data often remains locked even after the ransom is paid. And governments likely face a mountain of red tape and reputational harm if it’s discovered that tax dollars were used to pay cybercriminals.
One of the most significant developments in ransomware is the move toward double extortion. Attackers no longer just encrypt your data. They steal it first. That means even if you have solid backups and can restore your systems without paying a ransom, the attackers still have your data and can threaten to publish it or sell it on the dark web.
The first objective in a ransomware event should be containment. Affected systems should be isolated quickly to limit spread, preserve evidence and stabilize operations.
Contact your leadership, legal and risk teams immediately so that decisions about restoration, disclosure and external support are coordinated from the start. Outside counsel, forensic experts and insurers can help assess scope and obligations, while communications stay factual and focused on service continuity.
Systems should be restored deliberately from trusted backups, not rushed and once operations stabilize, the organization should review what failed and what needs to change to reduce future risk.
What Should Municipalities Do To Prevent Ransomware Attacks?
The best approach is to take a proactive stance to prevent the vulnerabilities that would invite ransomware in the first place.
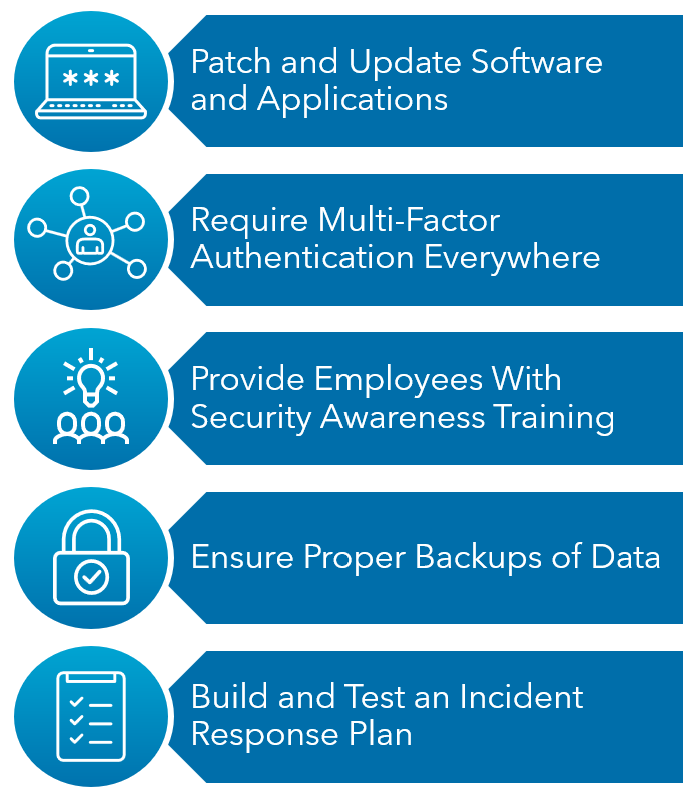
1. Patch and Update Software and Applications
In many cases of ransomware, attackers are taking advantage of vulnerabilities discovered in software and applications. So, it’s critically important that vendor-released patches rated as critical or high are implemented almost immediately.
Lower rated patches (medium, low or informational) are also important for system security, but these should first be reviewed for applicability and tested on a small group of machines before distributing to your entire environment.
Vendors often vary on how and when patches are released for their applications. Regardless, monitoring and reviewing these schedules is crucial. Some organizations use third-party patching software to help manage, prioritize and push patches to all of your systems based on applicability and criticality, but this process can also be performed manually.
2. Require Multi-Factor Authentication (MFA) Everywhere
MFA is one of the single most effective controls against ransomware. Attackers frequently gain access through stolen or compromised account credentials. If a password is the only thing that stands between an attacker and your systems and applications, you have a problem.
MFA should be enabled on every access point, cloud-based system, email and system interface. This is not an optional task anymore, and the cost of implementing MFA is a fraction of what a single incident or breach would cost.
3. Provide Employees With Security Awareness Training
Ransomware still spreads heavily through social engineering or phishing emails, when a message that appears legitimate tricks you into clicking on a link or providing valuable information. In the case of ransomware, when the user acts by clicking on a link, the ransomware is introduced onto the machine.
The world’s best security tools and software can oftentimes be circumvented by an employee unintentionally introducing ransomware or malware in an organization by clicking on content within a phishing email.
Consistently educating and raising the security awareness of employees against these types of attacks is a large step toward prevention. When employees are trained to be skeptical of unusual emails, they’re more likely to think before they click.
4. Ensure Proper Backups of Data
In the event ransomware infects and encrypts your organization’s data, the last line of defense and restoration is through the backups of your information. Some aggressive types of ransomware also look to encrypt backups, so it’s crucial to ensure there is a good working copy of your data.
Backups of data should be performed at least daily and need to be stored off-site physically (in a separate facility) or digitally in a cloud environment. IT personnel should also be receiving alerts or actively monitoring backup systems to ensure backup jobs are completed successfully.
Periodically, data from those backups should also be restored to ensure that information could be recovered in the event of a data loss.
5. Build and Test an Incident Response Plan
Having a copy of a plan that gathers dust on a shelf is unfortunately not enough. The organizations that can recover the fastest from ransomware or other incidents are the ones that have practiced their response before an incident happens.
This means running frequent tabletop exercises where leadership, IT, legal and operations walk through a simulated attack scenario. It also is important to have pre-negotiated retainers with cyber forensic firms and outside counsel so that you aren’t scrambling in the middle of a crisis.
Lastly, it also means defining roles and responsibilities for decision-making ahead of time so the critical first few hours of an incident aren’t spent trying to figure out who is in charge.
Learn More About Ransomware and How To Protect Your Organization
Ransomware is unfortunately not going away. The groups behind these attacks are well funded, technically capable and are constantly adapting. Municipalities may not always dominate cybersecurity headlines, but they remain prime targets for threat actors.
Attackers know that cities and counties hold sensitive data and run critical essential services and often operate with limited IT resources. However, the fundamentals of good cybersecurity practices still work. As attackers continue to search for new ways to exploit systems and information, municipalities must remain vigilant to prevent and detect these attacks by implementing good best practice controls.
To learn more about ransomware, how your organization can educate your employees or what measure you can put in place to protect yourself, contact your Warren Averett advisor or ask a member of our team to reach out to you.
This article was originally written on July 1, 2020, and most recently updated on April 28, 2026.

