The SOC 2 Catch 22 That Holds Small Companies in Place (And 7 Steps To Break Free)

For many small companies and startups, the SOC (System and Organization Controls) 2® conversation comes up at the worst possible time.
In many cases, a deal is in progress and the potential client is requiring your company to provide a SOC 2 report. Your sales team escalates the request, and leadership starts asking how quickly they can have a report in hand and back to the prospect.
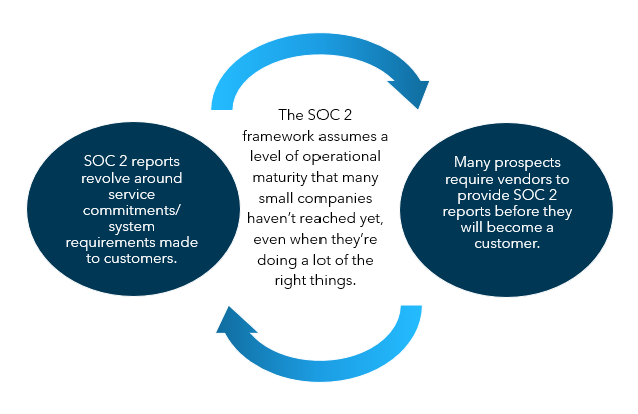
But there’s a catch-22.
SOC 2 is built around the service commitments a company makes to its customers (user entities) and corresponding system requirements necessary to provide the defined services to those customers. For mature companies, those commitments are normally documented in customer agreements, service level agreements or similar contracts. They define what the company says it will do and what policies, procedures and documented sets of controls exist to support those promises.
But early‑stage and small companies often don’t have that detailed structure fully in place because their customer contracts are still evolving and their commitments vary across clients. In some cases, the company may not have any customers at all yet.
And at the same time, their potential customers are still requiring a SOC 2 report before they will move forward.
In many cases, small companies hit a wall and the first attempt at a SOC 2 feels impossible. But the good news is that you do have options, and recognizing this early helps prevent spending time and money on an exam that can’t hold up once testing begins.
If your company is stuck in the SOC 2 catch-22, start with these seven steps.
1. Make a Cross-Departmental Team
Once the need for a SOC 2 report becomes urgent, responsibility is often pushed to one person inside the company. Most commonly, that person sits in IT.
The assumption is understandable. SOC 2 involves systems, security and access controls. The issue is that SOC 2 is not limited to information technology activity.
The SOC 2 criteria span many other operational activities, such as hiring and termination practices, background checks, employee training, codes of conduct, risk assessments, vendor oversight and management accountability, to name a few.
So when the entire effort is delegated to one role in one department, gaps show up quickly. Controls outside IT can be described incorrectly (or not described at all), which can have serious ramifications on your report. Evidence requests can also stall because no one person has end‑to‑end visibility into how the business actually runs.
It’s best to involve operations, IT, HR and management from the beginning, even if the team is small. That involvement reduces rework and shortens the path out of the deadlock.
2. Put Your Policies on Paper
Many small companies are doing more than they realize. You’re probably already conducting background checks, monitoring system access and onboarding and offboarding your team members thoughtfully.
Documentation of those activities is what is usually missing.
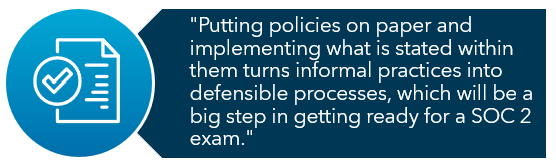
If policies, processes and internal controls are not formally documented, they are difficult to prove. If they cannot be proven, they cannot be tested. If they cannot be tested, the SOC 2 process cannot move forward.
This issue appears most clearly during evidence requests. The company may know a control exists in theory, but the service auditor has to have documentation showing that it exists, is implemented and that it is consistently applied.
Putting policies on paper and implementing what is stated within them turns informal practices into defensible processes, which will be a big step in getting ready for a full SOC 2 exam.
3. Use a Security Questionnaire as a Self-Readiness Check
If you’re unsure whether your organization is ready for a SOC 2 exam, start by completing a vendor security questionnaire in-house (before you start the exam process).These types of questionnaires are often required of customers when a SOC report is not available.
Security questionnaires typically force the same conversations a SOC 2 exam will. They require you to explain how access is controlled, how incidents are handled, how vendors are overseen and where responsibilities sit between your organization and third parties.
If those answers are hard to articulate, inconsistent across departments or dependent on a single individual’s knowledge, that friction will surface during a SOC 2 exam.
Using a security questionnaire this way reframes it from a compliance exercise into a diagnostic tool. Asking the question, “Can we provide evidence of what is stated in the responses” is often an eye-opener into what will be expected for documentation in the SOC 2 examination process.
Organizations that can complete a security questionnaire clearly and confidently with documented evidence are typically much better positioned to move through the SOC 2 process with fewer surprises, fewer follow‑up requests and less rework during the exam.
Following the self-readiness process with a SOC 2 readiness assessment by an experienced SOC advisor can help ensure an organization properly identifies the scope of the exam, its service commitments and system requirements, and the SOC 2 categories applicable to their services offered. They can also identify gap areas that need to be improved before the organization formally engages a SOC service auditor to perform the examination.
4. Consider What Type of Report You Need
The catch‑22 becomes most visible when organizations aim to go from nothing directly to a SOC 2 Type 2 report.
A Type 2 report evaluates controls over a period of time (e.g., over six months to a year) to give assurance the controls are suitably designed and operating effectively. That requires maintaining evidence for those repeatable processes that can be sampled and tested over that entire reporting period.
A SOC 2 Type 1 report looks at whether controls are designed and implemented as of a specified date (e.g., as of July 31). With documented controls, even limited activity can sometimes support that step.
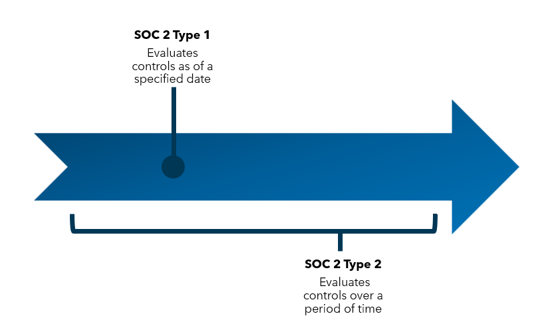
Understanding the difference allows leadership to select a SOC 2 report type that aligns with where the company actually is, rather than where deal pressure suggests they should be.
5. Consider Compensating Controls
Early‑stage companies frequently run into segregation of duties issues. One or two people may be responsible for the development, deployment and approval of a single task.
But that risk does not disappear simply because your company is small. Secondary review, documented approvals or shared oversight can mitigate the risk when traditional separation is not possible.
Acknowledging and mitigating these constraints allows progress without assuming immediate headcount growth.
6. Review Vendors/Service Providers and Responsibilities Carefully
Many small companies rely heavily on cloud service providers and third‑party vendors. That reliance often leads to the assumption that security controls are fully handled once a service is outsourced.
In reality, most cloud service providers operate under a shared responsibility model. While they secure underlying infrastructure, the customer remains responsible for how systems are configured, who has access, how activity is monitored and how incidents are handled internally.
This is why SOC 2 places meaningful weight on vendor management. Auditors expect companies to evaluate vendors before onboarding, understand what controls the vendor provides versus what remains internal responsibilities and reassess those vendors over time.
As a result, SOC service auditors will still ask detailed questions about systems hosted elsewhere. Even when infrastructure is outsourced, oversight, documentation and accountability typically remain internal responsibilities.
7. Resist a Quick Fix
When game-changing deals are at stake, speed becomes tempting. Off‑the‑shelf policies, templated reports, minimal reviews and “too good to be true” fees can appear to solve the problem quickly. And these solutions may even get a final SOC 2 report in your hands the fastest.
But these kind of options may be too generic or weak to actually meet the need beyond a surface level.
It’s important to remember that customers should be reviewing your SOC 2 report and critically assessing the seriousness of the company’s controls. Will you be able to defend a templated report when a prospect asks pointed questions about your controls and how their data is impacted?
If your customers are familiar with SOC exams and are asking you to produce one, they likely already know that it isn’t a quick process. Many will actually be willing to accept that you are taking steps through a SOC readiness process in order to have more mature controls in place and provide a higher quality report.
Choosing your SOC 2 service auditor carefully protects your credibility with prospects who understand how to read these reports and who will rely on them to make decisions about your organization. Like any other third party, ensure you are vetting the CPA firm that will be performing SOC services for you.
Perform due diligence on them like any other third party. Check their qualifications and experience, and inspect their peer review results on the AICPA Peer Review Website to see what the report rating was and if SOC examinations were included in the selection of engagements for review.
What Can Actually Move Your Company Toward a Successful SOC 2 Exam
Teams that break out of the SOC 2 catch‑22 tend to focus on alignment rather than acceleration.
They document what already exists. They involve the right internal roles. They select a starting point that matches their current maturity. They build controls alongside growth instead of waiting for growth to justify controls.
That approach replaces stalled deals with credible progress and gives leadership a position they can defend in front of customers, auditors and internal stakeholders.
To learn more, contact your Warren Averett advisor directly, or ask a member of our team to reach out to you.