Cybersecurity Planning vs. Cybersecurity Compliance: What’s the Difference?

Both cybersecurity planning and cybersecurity compliance are critical aspects of an organization’s information security posture and should work together to create a comprehensive security framework. Neither of these activities are one-time efforts but an ongoing process that must be monitored and managed.
But while cybersecurity planning and cybersecurity compliance are two interconnected concepts, they also have important differences that companies should know in order to have a strong security posture and meet any needed compliance requirements.
Cybersecurity Planning vs. Cybersecurity Compliance: Objectives
Proactive cybersecurity planning refers to safeguarding your company’s IT assets (including systems and data) from damage or theft from cyberthreats.
Cybersecurity compliance refers to understanding and adhering to applicable laws, regulations, policies and industry standards that apply to your organization. These may include laws related to data privacy, consumer protections and more.
Cybersecurity compliance aims to minimize legal, financial, reputational and operational risk by following relevant regulations, whereas cybersecurity planning seeks to strengthen a company’s entire security posture to protect against attacks.
While both ultimately seek to limit threats and protect companies and consumers against data loss, proactive cybersecurity planning considers your company’s larger IT scope and footprint, while cybersecurity compliance is more limited in scope and reactive in nature to conform to already-set guidelines.

Cybersecurity Planning vs. Cybersecurity Compliance: Activities
Proactive cybersecurity planning involves implementing protective measures, such as firewalls, encryption, intrusion detection systems and vulnerability assessments, all of which are designed to mitigate risk and reduce the ability for unauthorized access, data breaches and incidents.
Proactive cybersecurity planning is all about protecting systems and data by strengthening network security, endpoint protection, application security, data encryption, incident response, security awareness training and more. It involves implementing security technologies, conducting risk assessments, security audits and creating incident response plans to address security incidents effectively.
A great cybersecurity plan has three primary fundamental concepts:
- Confidentiality – Keeping information secure
- Integrity – Ensuring data is accurate and unaltered
- Availability – Being able to access data when needed and at the appropriate level of need

Cybersecurity compliance involves ensuring that the organization operates in accordance with legal and regulatory requirements, as well as internal policies and guidelines, and encompasses ethical and professional standards. Compliance should be a part of all businesses even if a specific compliance requirement is not dictated by an outside organization. Examples would be a company internet usage policy, email policy or company requirements for two-factor authentication.
Specific cybersecurity compliance requirements can vary depending on factors such as the industry sector, geographical location, data protection laws, financial regulations or specific contractual obligations. Common compliance and regulations are:
- Payment Card Industry Data Security Standard (PCI DSS)
- Health Insurance Portability and Accountability Act (HIPAA)
- Sarbanes-Oxley Act (SOX)
- Federal Trade Commission (FTC)
- General Data Protection Regulation (GDPR)
- Frameworks like Cybersecurity Maturity Model Certification (CMMC) that includes Defense Federal Acquisition Regulation Supplement (DFARS) 7012 and National Institute of Standards and Technology (NIST) 800-171
Cybersecurity compliance activities include conducting internal audits, implementing controls by developing and maintaining policies and procedures, providing training and education to employees, and providing evidence of adherence to regulatory requirements.
Because many cybersecurity compliance measures are designed to enhance a company’s security posture, there is some overlap between common compliance activities and common cybersecurity planning activities. For example, providing cybersecurity training to employees may be mandatory your organization, but it also may be part of the proactive plan you’ve elected.
Cybersecurity Planning vs. Cybersecurity Compliance: Approach
Cybersecurity planning is a proactive, layered approach that involves implementing preventive measures, security controls and continuous monitoring to detect and respond to potential threats and vulnerabilities.
Compliance is a more of a reactive approach that involves ensuring that an organization’s policies, procedures, and operations align with internal or external required regulations and standards.

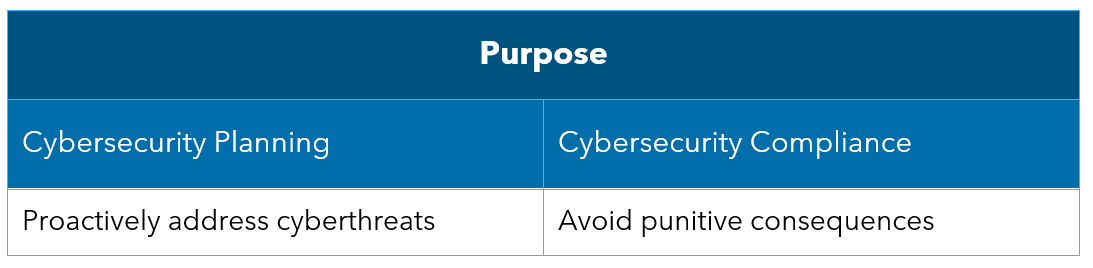
Cybersecurity Planning vs. Cybersecurity Compliance: Purpose
Because tactics (phishing emails, malware, social engineering, etc.) and the threat landscape for cybersecurity is constantly evolving, it’s crucial to stay ahead of potential risk. A great cybersecurity plan positions you for success because its key purpose is to proactively address these obstacles.
On the other hand, the key purpose of cybersecurity compliance is to avoid punitive consequences. Non-compliance can have serious ramifications for organizations, ranging from legal penalties and fines to reputational damage and loss of business. In some cases, individuals within the organization may also face personal liability.
Moving Forward with Cybersecurity Planning and Cybersecurity Compliance
If you aren’t sure where to begin, the best to way understand your current cybersecurity plan and cybersecurity compliance footprint is to have a third-party risk assessment.
Risk assessments help identify potential vulnerabilities, assess the impact of threats, determine the likelihood of attacks and help prioritize security measures to further tighten your cybersecurity posture. It provides a snapshot of where you are today, recommendations for what can be done to decrease vulnerabilities and a synopsis of what is missing from a compliance standpoint.
Common things found after a risk assessment are a lack of security patches to software and operating systems, lack of two-factor authentication or multi-factor authentication methods, improper firewall configurations and lack of written policies and procedures.
It’s always advisable to consult IT professionals in these areas for detailed guidance that’s tailored to your specific situation. Connect with a Warren Averett Technology Group advisor to start the conversation today.

