Malware vs. Ransomware: What’s the Difference?
With the emergence of cryptocurrencies and an increase in spear phishing campaigns, malware and ransomware threats are on the rise.
Is your organization positioned to prevent these kinds of cyber attacks? Do your company’s leaders know enough about them to make informed decisions in their daily work? Do you know what malware and ransomware really are (and what the difference between them is)?
Education is the first step toward preventing an attack on your business. Here, we’ve outlined the many differences between malware vs. ransomware and what your organization can do to protect against both.
Malware vs. Ransomware: The Basics
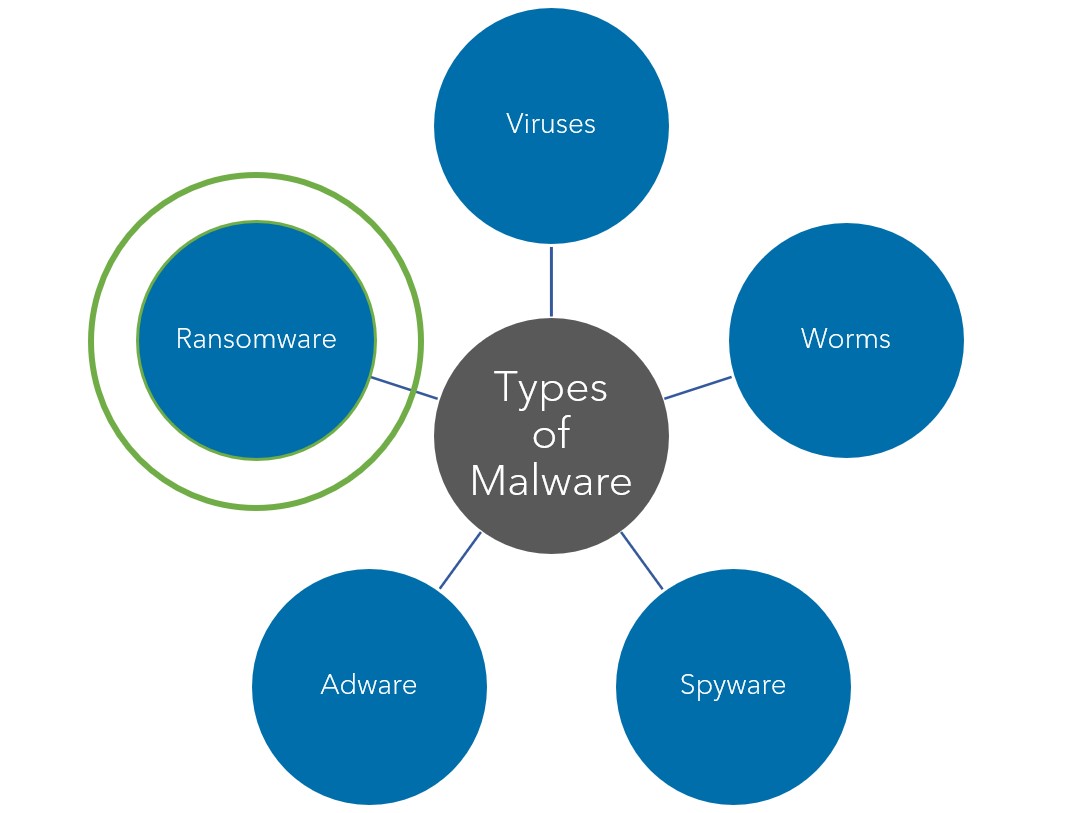
Malware (short for “malicious software”) is a blanket term that describes many different types of cyber threats, including viruses, worms, Trojan horse viruses, spyware, adware and even ransomware.
Malware refers to intrusive software, files or codes (typically delivered over a network) that infects, explores, steals or conducts virtually any behavior an attacker wants. Most commonly, it is used to infect systems and networks in order to gain access to sensitive information.
Ransomware is a specific type of malware. With ransomware, once the malicious software has been installed on a device, a hacker will cut off a victim’s access to files, giving victims the opportunity to regain access to these files only if a ransom is paid.
Because ransomware is a specific type of the broader category of malware, it may operate and function very much like other forms of malware. The key differentiator when it comes to malware vs. ransomware is the demand for payment to release captive files.
Malware vs. Ransomware: How It Works
Malware attacks function by spreading and installing malicious software on devices in order to steal money or sensitive information. Malware can spread and manifest itself in a variety of ways, and attackers can likely move quickly to get what they want by infecting devices or destroying files without contacting their victims.
Instead of destroying files, ransomware encrypts a user’s files so that they can no longer access them without the proper key—another key difference when it comes to malware vs. ransomware. Then, cyber attackers will contact their victims to demand a ransom payment for the decryption key.
Some of the most common ways malware and ransomware are initiated include phishing, unauthorized remote access or network vulnerabilities.
Malware vs. Ransomware: Red Flags for Attacks
Generally, in malware attacks, like Trojan horse malware, the malicious software is disguised as legitimate software and can remain undetected for a period of time. This means that continued damage can be done on an ongoing basis without a victim even realizing it.
On the other hand, victims of a ransomware attack often know right away that they are under attack. As soon as the hacker gains control of the device, the user or organization’s operations can become severely degraded or shut down entirely, and the hacker will likely soon reach out to make ransom-related demands.
Malware vs. Ransomware: Response and Recovery
Recovering from a malware attack will depend largely on the particular type of attack and how your business was specifically impacted. Because the range of impact can be so wide, it’s best to connect with an IT professional to discuss your remediation options.
Because the key difference between malware vs. ransomware is the ransom request, organizations affected by ransomware must first make decisions about whether or not to actually pay the ransom that the attacker is requesting. Businesses that suffer other types of malware attacks can move straight towards assessing and (hopefully) fixing the damage that has been done.
Is paying the ransom in your company’s best interest? It may still be a good idea to connect with an IT professional to help you assess your scenario and the risk involved to avoid the event of paying an expensive ransom and still not gaining access to your files.

Protecting Your Business Against Both Malware and Ransomware
Organizations can do a lot to protect themselves from both malware and ransomware. Because ransomware attacks are a specific segment of malware attacks, companies that prioritize protection against malware also position themselves to be protected against ransomware.
Businesses should deploy email-inspection technology that flags or deletes messages containing an infected attachment. But technology alone cannot protect you. Employees at every level across the organization should receive security awareness training and be aware of the latest cyber trends to ensure that they have the skills required to identify an attack.
For example, currently, amid The Great Resignation, one of the most common opportunities for malware and ransomware comes in the form of resumes, in which attackers send malicious attachments (posing as resumes) containing software that’s designed to steal usernames and passwords.
Having team members aware of scams like these will go a long way to prevent your company from falling victim to them.
Learn More About Malware vs. Ransomware
If you’d like to learn more about malware vs. ransomware, or if you need help protecting your business from future threats, speak with a Warren Averett Technology Group expert today.

