How to Identify and Address Gaps in Your Cybersecurity Compliance With a Cybersecurity Gap Analysis

Noncompliance with cybersecurity regulations is more than just an oversight. Regulatory fines, legal exposure and lost customer trust can create lasting damage to an organization. Yet, many companies still fall short of meeting cybersecurity compliance standards.
Does yours?
With constantly evolving and increasingly complex standards, how can you know for sure?
The gap between your current cybersecurity posture and what regulations require is known as a “compliance gap,” and it can exist in any organization. Even organizations with sophisticated cybersecurity programs can unknowingly operate with hidden compliance gaps—leaving the organization vulnerable to penalties and breaches.
Identifying and closing your organization’s cybersecurity compliance gaps is critical. And while compliance is ultimately your organization’s responsibility, you don’t have to start from scratch.
A cybersecurity gap analysis is a smart first step.

Identifying Your Compliance Gaps With a Cybersecurity Gap Analysis
A cybersecurity gap analysis is an evaluation conducted by a technology professional that methodically compares the state of your organization’s current cybersecurity posture against your applicable regulatory requirements. It helps you pinpoint where your measures fall short, prioritize remediation efforts and build a roadmap to full compliance.
A cybersecurity gap analysis is not meant to be a general, standardized assessment that can be applied to every organization in every industry. The most effective gap analysis should be customized to your industry, specific regulatory obligations and the risks targeting your company.
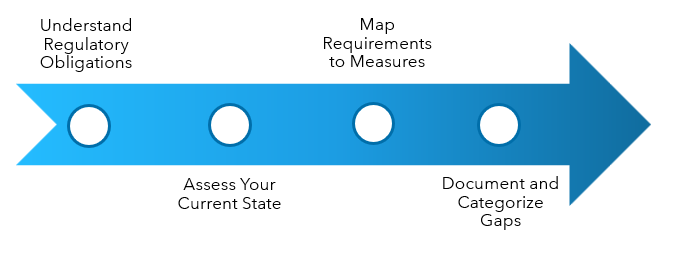
During a cybersecurity gap analysis, your technology advisor will:
1. Gain an understanding of your business-specific regulatory obligations
It’s essential to start with a complete picture of the regulations that apply to your organization and define the scope of the analysis. In cases in which your company intersects with different industries, it’s important to also understand how those regulatory frameworks interact with each other.
2. Assess your current state
Your advisor will work with you to determine which parts of your organization will be assessed, taking detailed inventories of your company’s assets, documentation, policies, safeguards, systems, databases, applications and data flows, as well as any network components that handle regulated data.
3. Map requirements to measures
Your advisor will then compare your regulatory requirements to your current state to identify your cybersecurity compliance gaps. Both regulatory knowledge and technical expertise are essential to ensure that the results are interpreted in the right business context and to account for your organization’s unique scenario.
4. Document and categorize compliance gaps
Cybersecurity compliance gaps are documented and classified according to severity, compliance risk level and potential business impact. Technical deficiencies (such as misconfigurations) and procedural deficiencies (such as insufficient policies or training) will be included as well.
Interpreting Cybersecurity Gap Analysis Results and Building Your Remediation Strategy
With the comprehensive cybersecurity gap analysis documentation in hand, you can begin to strategically remediate the gaps discovered.
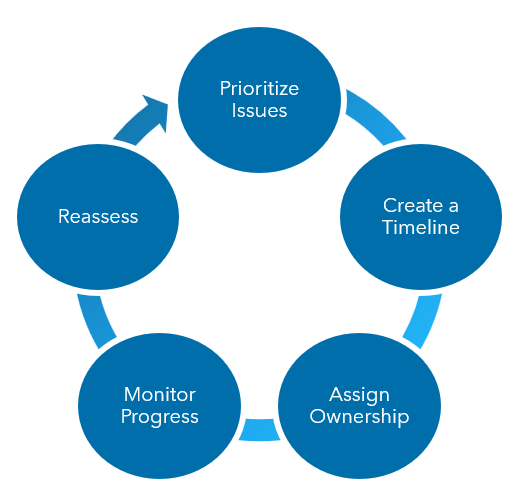
The plan you build to address identified discrepancies should have prioritized steps and clear, realistic timelines. For the best chance of success, the roadmap you create should first address foundational issues before tackling more advanced ones.
What deficiencies should take priority? Typically, the cybersecurity compliance gaps that can have the most business impact are:
- Gaps that could lead to fines, audits or legal actions
- Gaps that impact critical systems, sensitive data or customer trust
- Can impact business continuity and compliance standing
- Vulnerabilities for which there are known threats or active exploits
Your technology advisor can help you most accurately identify your organization’s unique priorities and establish a practical timeline.
To effectively execute a remediation plan, it’s important to assign ownership and accountability of specific steps to specific members of your team. Each gap that you identify should have someone assigned to it who ensures that the remediation takes place within a specified timeline.
To make sure that the remediation efforts stay on track and that any subsequent gaps are addressed as soon as they appear, you’ll need to monitor progress and reassess the remediations regularly.
Make Sure Your Compliance Is a Competitive Advantage
Compliance isn’t a checkbox: it’s a strategic imperative that can serve as a beneficial differentiator in your industry. To achieve and sustain the highest level of compliance, conducting a thorough cybersecurity gap analysis is a necessary first step toward a proactive and defensible cybersecurity program that helps protect your company from operational and financial dangers.
Connect with an experienced Warren Averett Technology Group advisor so that your company can efficiently navigate complex compliance requirements and effectively address your company’s cybersecurity compliance gaps.
