Cybersecurity Policy Development 101: What Should Be Included?

Each business should have good cybersecurity policies in place to protect your company’s information and reduce your risk when it comes to cyber-related activities.
But, if you don’t have cybersecurity policies, where should you start?
The Basic Cybersecurity Policy Development Framework
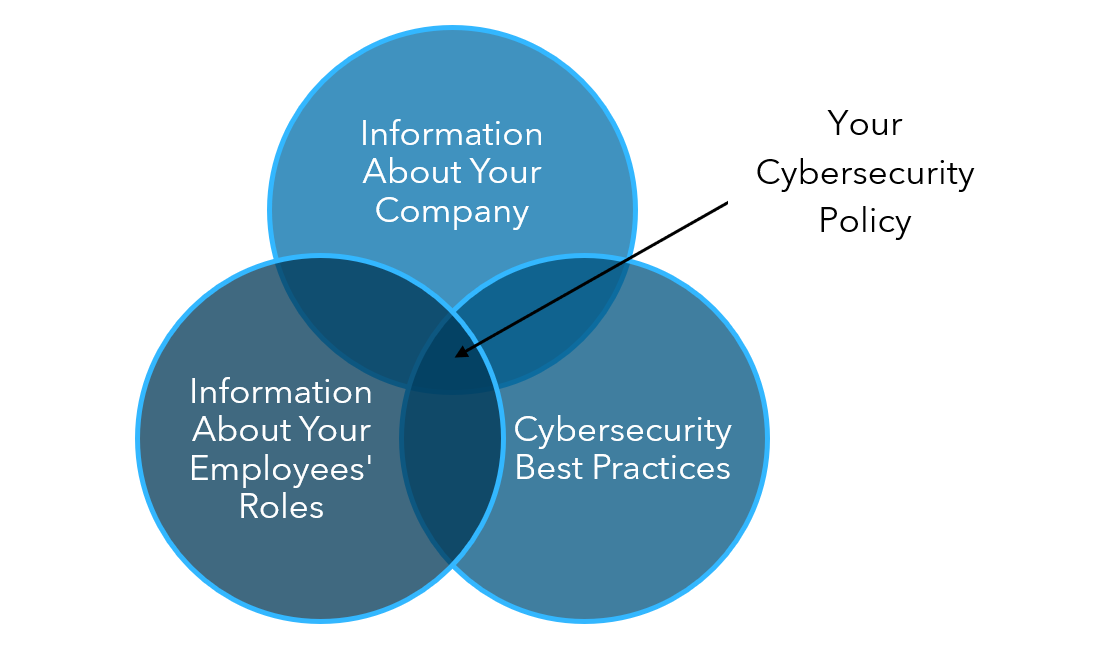
Developing a cybersecurity policy is all about combining your knowledge of your company’s specific needs and employees’ roles with cybersecurity best practices to create a policy that reduces risk for your organization.
Ultimately, a cybersecurity policy should set expectations and give employees the resources needed to follow the policy and protect your organization. So, the basic framework of cybersecurity policy development starts with considering:
- What cyber protection does your company need, and what risks do you have?
- What does your organization expect from your employees concerning those risks?
- How can you equip your employees to understand and comply with the cybersecurity policy?
The Four Basic Elements of a Cybersecurity Policy
Once you’ve considered what needs your cybersecurity policy will address and how your employees will be involved (and educated), you’ll have a solid base for establishing the individual pieces of your policies.
Your cybersecurity policy development will be customized depending on your organization’s business needs, the cybersecurity measures you have in place and the role your employees play, but all good polices have a few things in common.
Here, we’ve outlined the four main elements to consider when developing a policy for your organization.
1. Employee Education
Your employees are the first line of defense against cyberattacks and hacking, so their cyber education is a crucial component of cybersecurity policy development. Most of the time, you see this type of information in an acceptable use policy.
Your employees need to be aware of the many kinds of phishing emails and scams and how to identify them, as well as the proper ways to identify and report any cybersecurity threats if they do encounter them. However your company chooses to report threats should be readily accessible and easy for your employees to use.
2. Password Management
Considering password guidelines is a vital part of cybersecurity policy development. Some common password guidelines include:
- Passwords need to be changed every 60 – 90 days on all applications.
- Passwords need to be different on each application.
- Passwords need to be 15 characters or longer, must use a combination of upper- and lower-case letters, and must include at least one number and one special character.
While some of your employees may find it challenging to have a different password on each application, you can potentially make it easier by providing them with a password manager, multi-factor authentication, or facial or other device and application access method. Policies of this nature are generally in an access control policy or a password management policy.
3. Device Security
With more people working remotely, it’s difficult to know where your organization’s devices are—much less how secure and accessible they are. If these devices are stolen or misplaced, your organization’s data could be compromised, which is why device security should be a consideration in your cybersecurity policy development.
Consider requiring employees using personal devices to frequently lock their devices and avoid public networks if possible. Personal devices need their own set of guidelines to ensure the safety of your organization’s data. A policy in this area could involve an acceptable use policy, as well as an infrastructure management policy.
4. Privacy Settings
If your employees use personal devices to access your company’s network, their choices online can have an impact on your organization’s security. Encourage your employees to activate privacy settings on their personal email and social media accounts to limit the amount of personal information people can access. This is important if you allow employees to access work accounts from their personal devices, and information you place in an acceptable use policy will clarify your requirements.
Inform employees about the dangers of including private information on social media platforms. If employees are unwilling to remove certain information, such as birthdate or location, from their profiles, encourage them to only make this information available
![]()
Other Cybersecurity Policy Development Considerations
Depending on your organization’s IT structure, you’ll likely have other needs that should be addressed in addition to these four main elements, such as information about email use, general web access guidelines, accessing internal applications remotely, file sharing and more.
In addition, your cybersecurity policies should include information about IT functions within your organization, like who employees should contact if they need IT support or want to report a potential threat.
Having good policies in place—and making sure they are understood by everyone—is important to maintain the health of your company and to reduce risk. They can also make your employees aware of any additional resources that you have available that can help them with any IT needs, especially those pertaining to cybersecurity.
Get Help with Cybersecurity Policy Development and Connect with an Advisor
While you can’t totally eliminate human error, developing good cybersecurity policies and educating your employees can greatly reduce your chances of cyber risks and insider threats. Cybersecurity policies are crucial to protecting your business and its confidential information.
While this is just a general overview of cybersecurity policy development, it’s important to have policies that are specific to your organization’s needs and risks. If you need assistance developing cybersecurity policies for your organization, ask a Warren Averett Technology Group advisor to connect with you and start the conversation about how you can best protect your organization.
This article was most recently published on October 26, 2021 and most recently updated on April 25, 2025.