The Different Types of Phishing Attacks (And How to Recognize Them)

Phishing continues to dominate the digital threat landscape across the globe. No organization is completely immune from the threat, no matter how savvy their cybersecurity programs may be.
That’s because humans tend to be surprisingly inept at recognizing scams. As much as we may want to deny it, each of us is susceptible to being tricked or making a mistake.
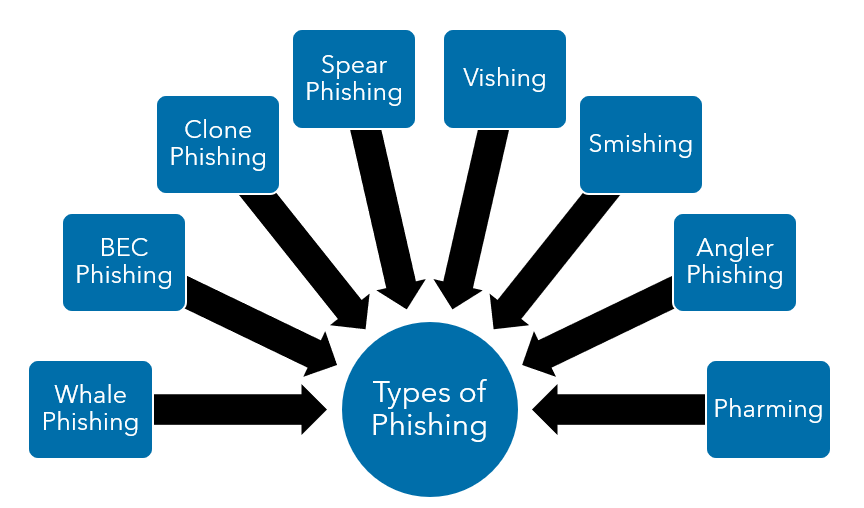
And as technology advances, scammers are engineering increasingly sophisticated techniques to compromise data and exploit companies for their own profit. This has resulted in the emergence of several different types of phishing attacks.
Because of our inherent curiosity, we have a tendency to make mistakes, and cybercriminals’ persistence to create new methods of deception, it’s essential to stay knowledgeable about phishing and all of the emerging tactics.
Educating your employees about the different types of phishing attacks is the first step in prevention because your team’s cybersecurity acumen is your organization’s first defense.
Here’s what your company should know about the different types of phishing attacks out there—and how you can spot them.
Download the eBook, How to Spot and Thwart Phishing Scams: A Guide for Businesses.
How To Recognize the Different Types of Phishing Attacks
Since phishing scams most often rely on human error rather than the strength of your protective systems, they can be especially hard to thwart.
While no company is totally safe from phishing, there are certain effective defenses that can be implemented—if you know what you’re up against. To that end, let’s examine the different types of phishing attacks commonly used today.
Whale Phishing
Whale phishing is a type of phishing attack that targets “whales”—lucrative targets, such as high-ranking corporate executives, CEOs and individuals with great value to an organization.
Such targets are far more prized to phishers than the average employee because a CEO’s credentials can be used to access and unlock valued data.
For instance, a compromised CEO’s email account can often be used to authorize fraudulent money transfers to a hacker’s account. It can also be used to access or request sensitive employee information, and that data can then be sold on the dark web or used for identity theft.
Also called whaling, this is one of the types of phishing attacks that can be particularly detrimental to a business’s reputation and finances.
Business Email Compromise (BEC phishing)
Somewhat like whaling attacks, cybercriminals typically use BEC scams to target personnel in accounting and finance departments.
A BEC phishing scam attempts to trick victims (such as finance officers) into transferring money from corporate accounts into unauthorized accounts.
This type of phishing attack is unique in that the attacker compromises the accounts of top finance personnel after monitoring email activity for a substantial amount of time to learn about their organization’s internal processes and payment procedures.
With this information in pocket, the attacker can craft a false email that deftly mimics one from a CEO or top executive directing the recipient to send a wire transfer to an external bank account of the attacker’s choosing.
Clone Phishing
This type of phishing attack is one of the hardest for employees to recognize and one of the most insidious scams.
In a clone phishing campaign, the attacker creates an almost identical replica of a legitimate email message in the victim’s inbox.
However, in this type of phishing attack, the scammer then replaces any attachments or URLs in the email with malicious ones and sends the email with a line explaining why the victim appears to be receiving the “same” message again.
The fake email is sent from an email address spoofed to resemble the legitimate address of the sender to trick victims into thinking that the email is genuine. In some more sophisticated variations, cybercriminals will design a cloned site with a spoofed domain to get victims to submit credentials or inadvertently download malware.
Spear Phishing
Unlike types of phishing attacks that target thousands or millions of users with a generic email, spear phishing is highly personalized to one individual.
For example, it might address your employees by name or even look like it’s sent from one of their contacts. By focusing on compromising a few high-value individuals, spear phishing is potentially one of the most lucrative types of phishing.
Phishers spend time acquiring and analyzing data from multiple sources and use the information they gain to craft spear phishing attacks with higher chances of success. Attackers typically include the target’s name, phone number, position, company address or other credible information to trick targets into believing that the phishing message is genuine.
Vishing (Voice Phishing)
Not all phishing scams are delivered via email. Vishing is a unique type of phishing in which cybercriminals (often impersonating a financial institution) call targets over the phone asking for account information, PINs or other credentials under the guise of an “official” purpose.
In other cases, a malicious actor may call your employee posing as a vendor, supplier or partner firm. The scammer urges the victim to divulge sensitive information or authorize a payment for a fake invoice.
Attackers can also execute a vishing campaign by setting up VoIP servers to mimic corporate entities and steal funds and sensitive data. A sophisticated example of a vishing scam occurred in 2019 when criminals, pretending to be Apple tech support, called victims and provided a number they could call to resolve a phony security issue regarding their iPhones.
Smishing (Text Phishing)
Smishing is the term used to describe a type of phishing attack that occurs via text, combining the words “SMS” and “phishing.”
The text message, which appears to originate from a trusted individual or organization, can be an effective way to convince individuals to take an action that provides the attacker with financial rewards or access to exploitable information.
Smishing scams are on the rise as people increasingly rely on text messages as a primary means of communicating, and they often appear to come from vendors that businesses know and trust—making it one of the most important types of phishing to be aware of.
In 2021, cybercriminals sent out smishing messages disguised as Amazon loyalty program rewards notices, FedEx shipment correspondence and United States Postal Service (USPS) updates. These smishing texts contained links to fake sites designed to steal payment card information and personal data.
Angler Phishing (Social Media Targeting)
This type of phishing targets your customers and can be damaging to your business’s reputation.
Individuals often turn to social media to get their customer support issues resolved, and criminals know that.
Angler phishing is an especially dangerous type of phishing for businesses because criminals create fake customer support accounts that promise to help your customers but secretly steal their credentials instead.
When fraudsters see a customer contact your business, they hijack the conversation by responding directly to that customer using their fake support page.
Fake business profiles are created and used to send instant messages, tweets, posts, links to cloned websites and fake URLs to persuade targets to download malware or divulge sensitive information.
Pharming
Some cybercriminals take an entirely different approach to phishing. Rather than craft fraudulent phishing messages, these bad actors use pharming—a type of phishing attack that is perpetrated using DNS (domain name system) hijacking, DNS spoofing and DNS cache poisoning techniques.
A pharming attack is designed to compromise a DNS server and change the IP address that is associated with a legitimate URL.
With pharming, users who click on the legitimate URL will be redirected to a different IP address—one that points to the attacker’s malicious website of choice.
Pharming is an advanced type of phishing because it’s hard to spot and designed to capture large swaths of users at once.
How To Protect Your Business From the Different Types of Phishing Attacks
Educating your employees about the different types of phishing can go a long way toward preventing breaches. It’s also important to be aware that cybercriminals are constantly leveraging new technology and techniques to design subtle and increasingly sophisticated types of phishing attacks. It can be hard to stay on top of it all.
If your business could use help tracking scams to increase your chances of avoiding a catastrophic phishing scam, Warren Averett Technology Group can help. We provide ongoing security awareness training that can bolster your company’s chances of avoiding a serious cyberattack.
We’ll design and structure security awareness training that is comprehensive and focused on simulating real-world scenarios. We can also help you understand more about how to secure your IT environment, so schedule a meeting with us today.

