Secure Cloud Hosting: What It Is, How It Works and Where to Start

Global cyber attacks have increased 125% year-over-year—and there’s no slowdown in sight. So, for small to medium-sized business (SMBs), securing your network’s data is incredibly important.
Secure cloud hosting is quickly becoming essential to ensuring the lasting success of your business.
Whether you already have a cloud solution in place or are just getting started, secure cloud hosting offers numerous ways to strengthen your network, server and data security. Here, we outline the basics of what secure cloud hosting is, how it can prevent cyber attacks on your organization and how you can get started.
What is Secure Cloud Hosting?
In its most basic level, secure cloud hosting refers to the third-party act of securely running and maintaining a network of servers and data files on a company’s behalf.
This means the files, images and videos that you save on “the cloud” are actually being stored in a secure, offsite location on servers owned by cloud service providers.
We commonly refer to these physical servers as “the cloud” because users can gain access to their files from authorized devices with internet connectivity, making it seem as though it’s being retrieved from thin air.
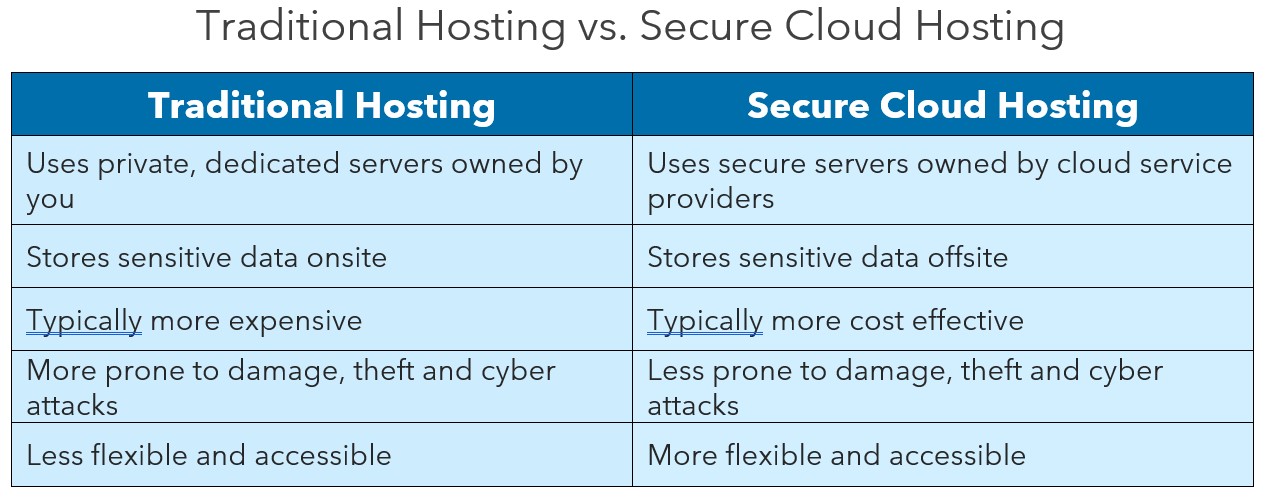
Compared to the traditional hosting model, which uses private dedicated servers (usually kept onsite) to secure sensitive information, there’s less risk and cost associated with cloud hosting. The main things that differentiate secure cloud hosting from the traditional model are:
Safer Storage
Cloud servers are usually located in secure warehouses that most workers don’t have access to, leading to less data corruption or theft. Cloud providers also offer file replication services to store multiple copies of your critical data files in multiple locations throughout the cloud which can be quickly recovered. This prevents you from losing everything in the event of severe weather, floods, fires or a cyber attack.
Cost Effective
Secure cloud hosting is typically more cost effective than the traditional model because you have the option of right-sizing your servers’ capacity to the required size. This keeps you from having to over-purchase more capacity than you need. Cloud hosting also provides more immediate and timely access to scalable servers, offering attractive upgrade options to support the ongoing scaling and right-sizing of your servers.
Providers also incur the cost of all the new security tools you will have access to as their client, and they are consistently pushing out updates so you are always getting the most bang for your buck. Their platforms have hundreds of services and security measures that smaller companies would likely not be able to afford on their own.
Companies that want to leverage tax benefits and minimize their CapEx expenditures, consider secure cloud hosting an attractive option by consuming their compute capacity as a monthly OpEx fee. That’s right, cloud computing might even save you money on your taxes!
Increased Flexibility and Connectivity
Secure cloud hosting also allows for greater workplace flexibility, especially with so many employees working from home these days. With cloud hosting, employees can gain access to their network’s files from anywhere by simply connecting to the internet through secured measures.
Storing files on the cloud also enables real-time collaboration of shared files such as presentation files, spreadsheets, source code files, etc. Files can be quickly checked-out and checked-in to ensure all team edits are captured and reviewable among the team. This can also decrease the clutter on your devices, leading to faster connectivity and increased processing power.
Increased Security Resources
Because secure cloud hosting providers are usually large corporations, they’re able to afford the cost of equipping their servers with powerful resources and security measures to keep your data highly secured. Their robust resources can provide protection against ransomware attacks, enhanced anti-virus protection and so much more. They can also take on the responsibility of ensuring your data is fully encrypted, highly defended and repeatedly backed up in multiple copies.
How Does Secure Cloud Hosting Prevent Cyber Attacks?
Most cyber attacks occur using malware and phishing techniques, which can grant a cyber criminal access to sensitive information, but only on your own device(s).
During an attack, cyber criminals may install ransomware designed to freeze your device and corrupt your files, blocking access to your computer’s data until a sum of money is paid. If all your data is only stored on your computer in a traditional hosting model and your company experiences a cyber attack, it could be detrimental to your business.
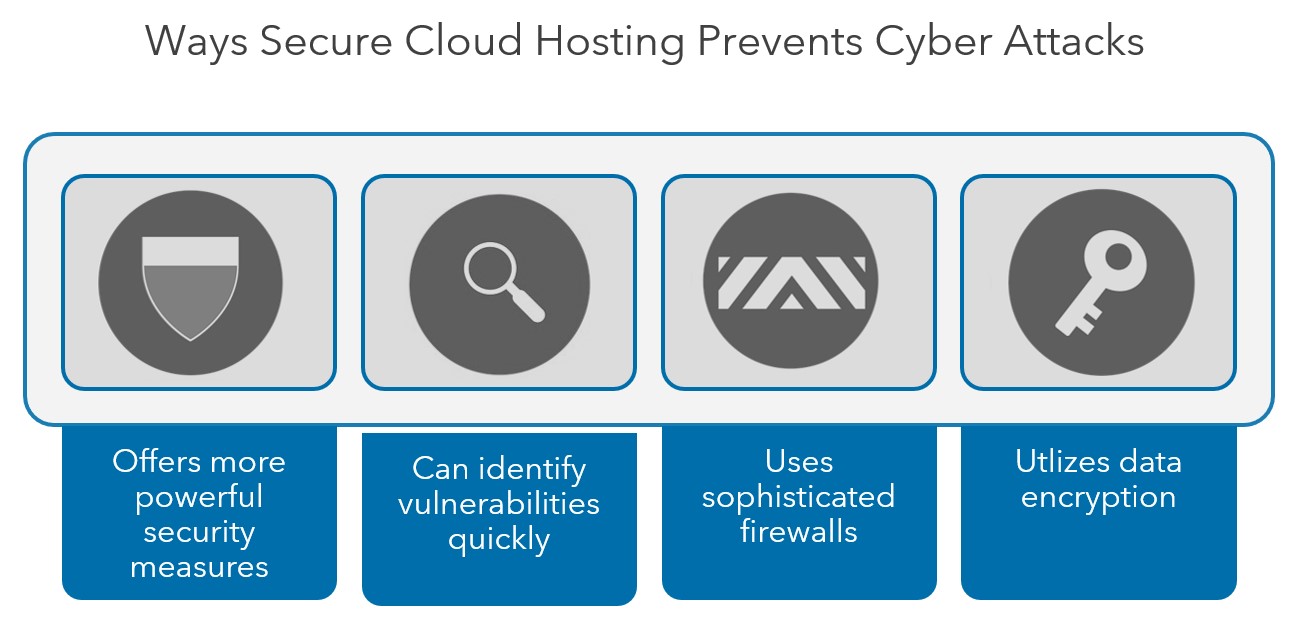
On the other hand, secure cloud hosting providers can provide more powerful resources and security measures than traditional hosting models. They can take on the hassle of tasks like server maintenance, consistent security updates, auto-patching, system redundancy and backing up data.
Some secure cloud providers are even using artificial intelligence, or AI, to perform cybersecurity assessments. These programs rely on built-in algorithms to seek out and identify vulnerabilities in security measures so businesses can respond quickly if their data does become compromised.
Firewalls are also widely used to protect data because they set rules for all incoming network traffic, providing a line of defense against cyber attacks. These rules are designed to filter out suspicious or unwanted traffic, ultimately determining what can come through the wall and what gets blocked.
Lastly, a crucial cybersecurity measure your secure cloud hosting provider should offer is data encryption. With encryption, it’s much more difficult for cyber criminals to access your sensitive information.
An Example of Secure Cloud Hosting Protection
A real-life example of this came in March of 2021 when a new strain of ransomware, now known as DearCry, impacted the Exchange servers used by hundreds of thousands of organizations around the world, from governments and banks to healthcare and charities.
There was one group, however, that didn’t have to worry—those that used the provider’s cloud-based services. Because the vulnerability was localized to on-premise implementations (or those using traditional hosting), the organizations that were using the cloud-based service were excluded from attack.
In the end, the cloud saved thousands of businesses from a cyber attack.
How Can I Get Started With Secure Cloud Hosting?
The good news is that you’ve already begun when you started reading this article. Research and understanding your options are the first steps in finding a secure cloud hosting provider. Here are a few things to know about the top three largest secure cloud hosting providers on the market:
Microsoft Azure
Debuting in 2010, Azure is one of the fastest-growing cloud platforms. It has more than 200 products and cloud services designed to help solve today’s challenges and prepare for the future.
This platform allows you to build, run and manage applications across multiple clouds with the tools of your choice. It also provides scalable, cost-effective solutions to work with your budget.
Since Microsoft is committed to the highest levels of trust, transparency standards and regulatory compliance, you can rest assured that security and privacy are foundational to Azure.
This, plus the fact that it’s not limited to Windows-based services, could explain why more than 95% of Fortune 500 companies are using this platform.
Google Cloud Platform (GCP)
Also debuting in 2010, the GCP offers over 100 services that span from computing and networking to big data and more.
Despite its smaller size, GCP can offer a robust set of services using Google’s core infrastructure, data analytics and machine learning, and it’s designed to support any kind of application. Its foundation is built upon a commitment to open source and industry-leading price performance.
Amazon Web Services (AWS)
Released in 2006 as an internal cloud offering, AWS has evolved into one of the most mature cloud platforms to date. It now offers over 200 fully featured services, which cater to practically any type of organization and currently serves millions of users.
AWS also uses a serverless application model, which is changing the way companies do business by enabling them to deploy software and applications much faster and more frequently than other competitors.
What if I’m Already Using the Cloud?
If you’re already using secure cloud hosting, you can still boost your cloud’s security by enlisting the help of a third-party cybersecurity assessment provider. This company should be different from your secure cloud hosting service provider so that their servers and software can be regularly tested by an outside party to make sure your data is safe from hackers.
Warren Averett Technology Group offers cybersecurity assessments, cloud-based solutions, IT security solutions, managed services and IT remediation to elevate your system’s infrastructure and keep it running smoothly. Our team of IT and security professionals has helped companies of all types and sizes strengthen their networks.
If you’re interested in learning more about secure cloud hosting, or the other services we provide, ask a technology advisor to reach out to you to get the conversation started


