Do Your Employees Use Cell Phones for Work? [What Companies Should Know about BYOD and Mobile Device Management]
The way companies and their employees handle day-to-day operations has shifted dramatically in a short amount of time.
Even before the pandemic, employees were sometimes expected to be available outside of typical business hours. Now, the rise of hybrid and remote work has fueled an even greater increase in employees’ use of cell phones, tablets and other mobile devices for business use.
While mobile devices were once almost exclusively owned and managed by a business, it’s now more common than ever for employees to bring their own devices (BYOD – bring your own device), like cell phones and tablets, to connect to corporate resources.
Most would view this as a win-win scenario for both the company and employee, but proper management of those devices is critical for it to truly be beneficial.
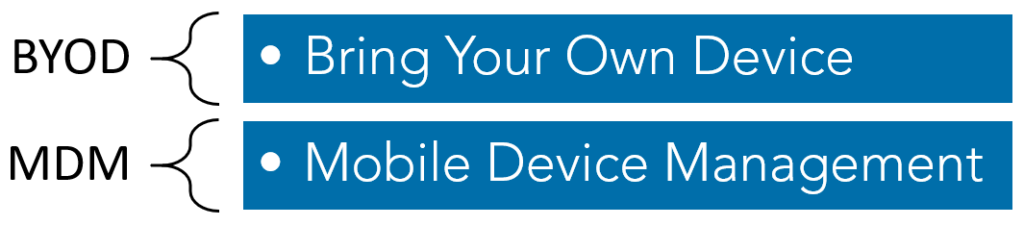
Understanding the Risk in BYOD and the Need for Mobile Device Management
BYOD inherently introduces some risk to your organization. The more people and devices that are connecting to your network, the greater the chances are for a breach.
A breach of company and/or customer data has proven itself to be quite costly for businesses, in addition to the reputational hit often sustained within a company’s industry.
While policies and procedures are a good starting point for BYOD management, there are many other additional security considerations.
- Can the security on an iPhone be managed in a similar fashion as an Android-based device?
- What native security measures are deployed within these devices, and does it meet the company’s acceptable level of organizational risk?
- How should a business maintain a separation between an employee’s personal content and the company’s corporate content?
The Importance of Mobile Device Management Tools
A good mobile device management (MDM) tool can help to bridge the gap between the convenience of employees utilizing their own devices and maintaining an acceptable level of security required by a company.
MDM tools are often cloud-based tools that function as an inventory system to track all mobile devices and serve as a hub to distribute security policies to the device.
In the event a user attempts to bypass security restrictions (e.g., remove the password setting), the mobile device management tool automatically detects non-compliance and prevents access to any company resources.
The functionality and availability of security policy restrictions will vary widely between different MDM tools. So how can you know what your company should expect from its MDM tool to effectively protect your business?
Seven Questions to Ask about a Mobile Device Management Tool if Your Company Allows BYOD
Below are a few considerations when either evaluating the functionality of an MDM solution or ensuring that your existing MDM solution and procedures are appropriately configured and effective.
1. Does your mobile device management tool account for differences among devices?
There are many different types of phones and tablets which all have varying levels of native security functionality. These differences must be understood and accounted for when designing device protection policies for MDM tools.
For example, all of the information that resides on Apple devices is encrypted by default, whereas Android and Blackberry devices required additional configuration to encrypt the information.
2. Does your mobile device management tool have strong password requirements?
Passcodes or PINs are essential to ensuring the sensitive data on the device remains protected.
This requirement may also be extended to biometric authentication (retina or fingerprint scans), which resides on most newer phones today and can provide a truer form of user identification than a PIN or passcode.
A PIN or passcode, if enforced, should be no less than four digits (preferably six) and should disallow the use of consecutive digits or easy to guess passwords (e.g., 0000 or 1234).
3. What is the procedure when a device that contained company data is lost or stolen?
With most mobile device management solutions, remote wiping of the device can be easily performed. In addition, depending on configuration settings, a device can sometimes be tracked to help determine its location.
When considering employee-owned devices, remote wiping and location tracking can be beneficial to the company, but it can also draw concerns from employees, especially when considering the balance between personal privacy and company property. If your company is remote wiping a device, does that also erase all information on the employee’s phone, which may include an individual’s photos, text messages and other personal data?
Many mobile device management tools allow company data to be stored only within a container on the device, which is encrypted and allows remote wiping of only that container if a device is lost or stolen. It’s crucial for your company to have an agreement with employees outlining what’s acceptable by both parties.
4. Does your mobile device management tool alert your company to unrestricted access?
Jailbreaking and rooting of devices should be disabled, and alerts should be created within the MDM policy to notify IT personnel if these acts are attempted. These methods of modifying a mobile device allow a user unrestricted access to the phone’s operating system, thus bypassing all security restrictions defined within the MDM tool.
5. Does your mobile device management tool consider device operating systems?
Device operating system restrictions should also be considered as a policy management item. Just as computer operating systems age over time and are no longer supported by the vendor, phone operating systems may go through a similar aging process.
As vulnerabilities are discovered, device manufacturers release updates and patches to remediate them. Therefore, a company’s MDM policy should limit the versions of mobile operating systems to only those that are vendor-supported to prevent malicious users from taking advantage of vulnerabilities that may exist on company-owned or employee-owned devices.
In addition, some device manufacturers now allow users to test a beta version of an operating system. Beta testing versions are not meant for general public release and may contain many vulnerabilities that may make data on the device susceptible to compromise.
6. Does your mobile device management tool protect against app vulnerabilities?
Once thought to be limited only to computers and servers, malicious users are now focused on vulnerabilities and malware that target a mobile device’s app store (e.g. Apple’s App Store or Google’s Play Store).
The vetting and security review requirements vary widely per app store. For example, Apple’s App Store requires an extremely thorough review process, which considers the safety, performance, security and design of the application.
However, recent statistics have shown that over 60% of Android apps available contain security vulnerabilities and on average Android apps each have 39 security vulnerabilities.
When designing security policies for mobile device management tools, a whitelist should be developed to ensure that users are only allowed to utilize apps that are developed by reputable businesses and deemed to be generally safe for use.
While lesser known or “free” apps are typically the culprit for security issues, this does not exclude doing your proper due diligence for more popular apps as well.
Apps such as TikTok or Facebook have recently been under scrutiny for improper information sharing and privacy concerns.
7. Does your company have a Mobile Device Agreement?
In addition to strong mobile device controls, the device users (your company’s employees) and their activities should also be considered. The most appropriate method of finding common ground between a user and the company is through a Mobile Device Agreement or an Acceptable Usage Agreement.

Acceptable use of mobile devices (social media usage, app restrictions, use during work hours, etc.)Prior to granting access for mobile device usage, employees should be required to acknowledge and sign an agreement of BYOD-acceptable use. These agreements may vary, but a few common things to consider are:
- User responsibilities and corporate responsibilities
- Reimbursement policy (if applicable)
- Supported and unsupported device types
- Security configurations and controls (strong passwords, logouts after inactivity, lockouts after invalid password attempts, ability to remotely wipe, device encryption, etc.)
- Company’s right to monitor and protect
- Policy enforcement and consequences of policy violation
Likewise, during the employee termination process, having controls to ensure your company and customer data is timely removed from personal phones and devices is crucial. Mobile device procedures should be built into termination checklists so that, as an employee is exiting the organization, all stored company data, email, cached data and access to resources is removed from personally-owned devices.
Moving Forward with BYOD and Mobile Device Management
The technology shift from traditional business equipment to mobile devices is here to stay, and it will be a fixture in the way companies perform business functions in the future. BYOD and mobile device management should be top considerations for organizations whose employees use cell phones or other mobile devices for business use.
Embrace these technologies, as they can offer invaluable benefits to both the employee and business. As with any technology, companies must plan proper procedures and develop control activities to mitigate the risks associated with your sensitive customer and corporate data being more mobile.
This blog was originally published on June 4, 2019 and was most recently updated on July 23, 2021.