Spear Phishing vs. Phishing: What’s the Difference?

The prevalence of phishing is increasing—and so is what’s at stake.
In 2020, 75% of organizations around the world reported at least one successful phishing attack, and a majority of these attacks were attributed to spear phishing.
You’ve probably heard of traditional phishing before, especially with the threat of attacks skyrocketing in recent years, but are you aware of the specificities of spear phishing? Could you tell the difference between spear phishing vs. phishing?
Understanding these nuances can help your organization better identify these types of attacks, educate your employees and prevent cyber crime. That’s why we’ve outlined the key differences of spear phishing vs. phishing—and how you can protect your company against both.
Download the eBook, How to Spot and Thwart Phishing Scams: A Guide for Businesses.
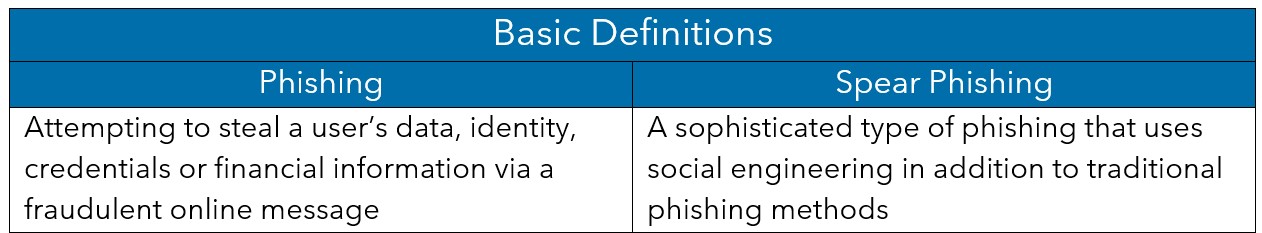
Spear Phishing vs. Phishing: Definitions
To understand the intricacies of spear phishing vs. phishing, it’s important to first grasp the basic differences.
Phishing is the fraudulent practice of attempting to steal a user’s data, identity, credentials or financial information. The goal of a phishing attack is usually to trick a victim into opening a fraudulent online message that’s been disguised as a trusted contact. Through this cyber connection, attackers are then able to steal a victim’s personal information.
Spear phishing is a specific type of phishing. It’s considered to be a more sophisticated version of traditional phishing because of its use of social engineering and media. Because spear phishing is more advanced than traditional phishing, it has the potential to be more damaging for your company if it goes undetected.
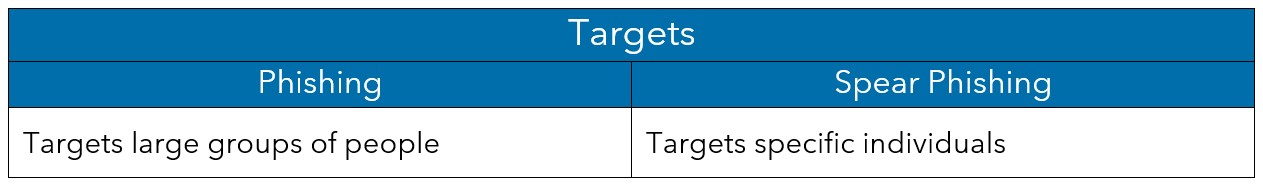
Spear Phishing vs. Phishing: Targets
Traditional phishing doesn’t target a specific individual, but instead casts a wide net to several potential victims. Traditional phishing attempts will impersonate a trusted source, but they are not personalized to the recipient.
Spear phishing targets specific people within a particular organization.
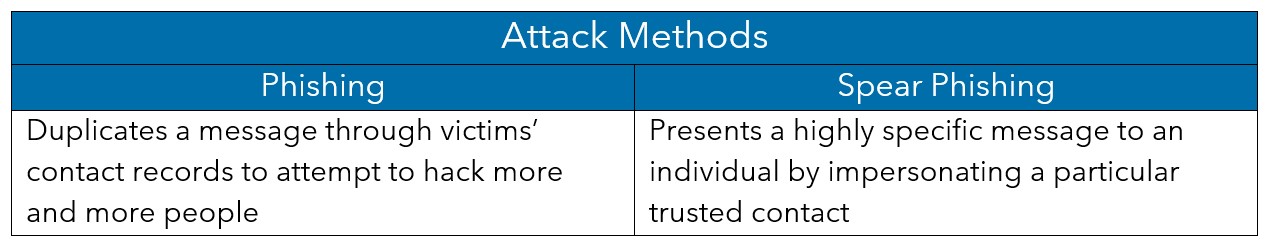
Spear Phishing vs. Phishing: Attack Methods
Because traditional phishing messages don’t target specific individuals and because these messages are usually duplicated through victim’s contact records, they are relatively generic in their messaging. Most phishing emails will be sent with an urgent plea that would be applicable to many people—like to reset your password with a vendor.
On the other hand, before a spear phishing trap is set, spear phishers will collect data on the internet, social media and the dark web about a particular employee or a company to create a highly specific and believable message—likely impersonating a specific coworker or referencing an actual company initiative.
In the last 10 years, a substantial amount of information has been added to the internet about organizations and the people who work for them. This online content and social media activity gives the spear phishers everything they need to know to impersonate a trusted figure within an organization.
Phishers use this accurate information to increase the target’s false sense of security before attempting to steal their company credentials or gaining access to their company’s database.
Spear Phishing vs. Phishing: Red Flags
Traditional phishing attempts are often laced with grammatical errors, confusing information and awkward language.
However, it can be difficult to spot a spear phishing email because the details inside the message usually contain somewhat accurate and convincing information.
In either case, it’s important to check the sender’s email address for accuracy. Pay close attention to each character because it can be hard to spot the difference between a legitimate address and one that is not if only one character has been added or removed.

Prevention and Protection Against Spear Phishing and Traditional Phishing
While there are many differences in tactics, targets and methods, when it comes to spear phishing vs. phishing, the most effective prevention methods you can implement to protect your company are largely the same—employee training and technical safeguards.
Institute Employee Training
One of the most important things your company can do to prevent any type of phishing is to train your users to spot, delete and report suspicious messages.
But the truth is that even the most well-trained, observant user has the potential to fall victim. As social media use explodes, working from home becomes the norm and new challenges arise, the harder it will be to defend ourselves.
Implement Technical Safeguards
Now is a critical time for businesses to complement employee training with technical solutions to prevent phishing and spear-phishing emails from ever arriving in your users’ inboxes. It’s much easier to defend yourself against an attack than come back from one.
Learn More About Spear Phishing vs. Phishing
If you’d like to learn more about spear phishing vs. phishing, or if you need help protecting your business from phishing attacks, speak with a Warren Averett Technology Group expert today.

