What Happens After a Cyber Incident? (Managing the Impacts and Navigating Recovery)
Cyber incidents are becoming so common in today’s digital landscape, it’s almost certain that your organization will experience some type of incident or attack (if you haven’t already).
The best way to withstand a cyber incident is to invest in proactive prevention. But what happens if an attack on your company is actually successful? What should you do if you suspect that your company is experiencing a cyber incident? And what is the road to recovery like in the aftermath?
From launching an initial response to applying the lessons learned, here’s what your organization could realistically expect on the path to recovery after a cyber incident occurs.

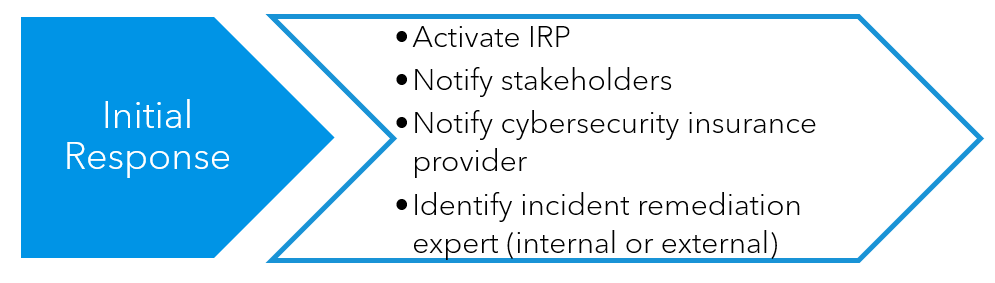
Initial Response
As soon as you know that a cyber incident has occurred, it’s time to activate your organization’s incident response plan (IRP).
This carefully planned and well-documented guide will serve as your cyber incident playbook. It details everyone who is expected to have a role in responding to the threat, his or her specific duties and what critical steps should be taken before, during and after a cyberattack. Having a relevant IRP documented ahead of time is the best way to know quickly how to respond effectively to a cyber incident.
However, if your company does not already have an IRP in place when a cyber incident occurs, your first action should be to notify all business stakeholders and your cybersecurity insurance carrier of what has happened. If your company doesn’t have internal resources trained in incident remediation, you should also contact a company that provides such services to guide you through the process.
Some cybersecurity insurance carriers have their own response team that can assist in the incident response processes.
Containment and Investigation
To limit the spread of the cyber incident’s impact, isolate the infected systems as soon as possible. Depending on the type of incident, this can include disconnecting services, shutting down services, changing login credentials or blocking or rerouting network traffic.
A cyber incident can have a cascading negative impact that could touch every aspect of your company, so it’s also important to consider how to mitigate the impact to your operations and reputation.
Once the impact is contained, gather evidence from the impacted systems, network devices and other relevant sources. The tracks that malicious actors leave behind in network traffic logs, emails, protocols and more will have to be examined for any subsequent recovery and forensic investigation.
Determine the depth/impact of the incident and prioritize response activities based on the criticality of the impacted systems. The goal is to eliminate the root cause of the incident and get your systems safe and operational as soon as possible.
Assess factors like the sensitivity of data impacted, how many end users were impacted and more to determine which systems should receive prioritization.

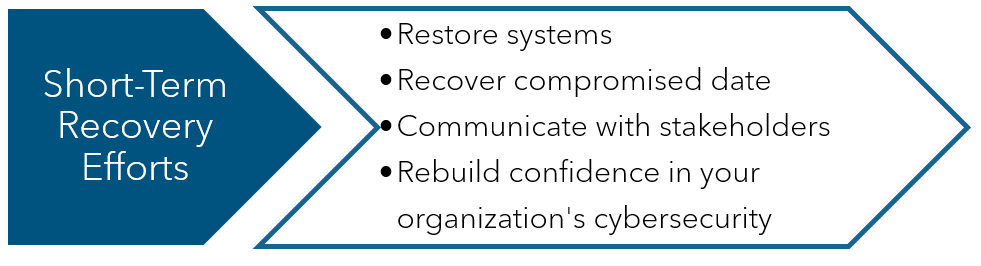
Short-Term Recovery Efforts
Getting back to business as soon as possible will require that you first restore the impacted systems and recover compromised data. This can be accomplished using data backups or advanced data recovery methods to restore lost files or access files encrypted by ransomware.
At the same time, you should be communicating with stakeholders, including employees, customers and other organizations that may be part of your supply chain. The communication should be clear and accurate, giving as much information as necessary about the steps you’re taking to be cybersecure again and to restore operations.
Rebuilding confidence in your company’s cybersecurity is a necessity.
Long-Term Recovery and Prevention
Experiencing a cyber incident forces you to see where improvements can be made to your organization’s cybersecurity infrastructure.
You’ll likely need to update some of your security practices, such as employee awareness and training, password protocols, the use of personal devices for organizational tasks and multi-factor authentication. Establishing a cadence of conducting continuous security monitoring and regular assessments can also help lower your organization’s risk of having another incident and improve your incident response planning.
In extreme cases, you may consider completely overhauling your organization’s cybersecurity plan to more effectively prevent incidents in the future.

Learn More About Recovering From a Cyber Incident
Cyberthreats have become incredibly sophisticated, and they will continue to evolve as malicious actors seek to gain access to unsuspecting organizations’ IT environments and assets.
How well and how quickly your company can respond to and recover from a cyber incident will be influenced by factors like the severity and complexity of the attack, the strength of your cybersecurity measures and how well your organization was prepared to respond.
Using a well-prepared IRP can reduce recovery time; having great cybersecurity recovery processes in place and having a strong cybersecurity advisor can help simplify the recovery process before an incident even occurs.
Connect with a Warren Averett Technology Group advisor to learn more about how you can protect your business from cyberthreats.

